The global pandemic situation has changed the course of the world and forced the people to take another leap towards adaption. We have adapted our ways of working in recent months, and it has liberalized our methods. However, it won’t change the fact that many work-from-home employees don’t have adequate security solutions.
Why do work-from-home employees have to maintain security?
Most of the work-from-home employees have skipped going to work due to the pandemic situation. Multi-million companies have advanced security systems in place, so third-party invaders cannot penetrate the walls. However, most of the home laptops & desktops don’t have corporate-level security and have to depend on an operating system provider for it, you should look into some of the best Ergonomic Desks, if you work from home. We are going to list down several ways for the users to protect themselves from invaders. You may learn more about network visualization next.
1. Secure your connection with a VPN
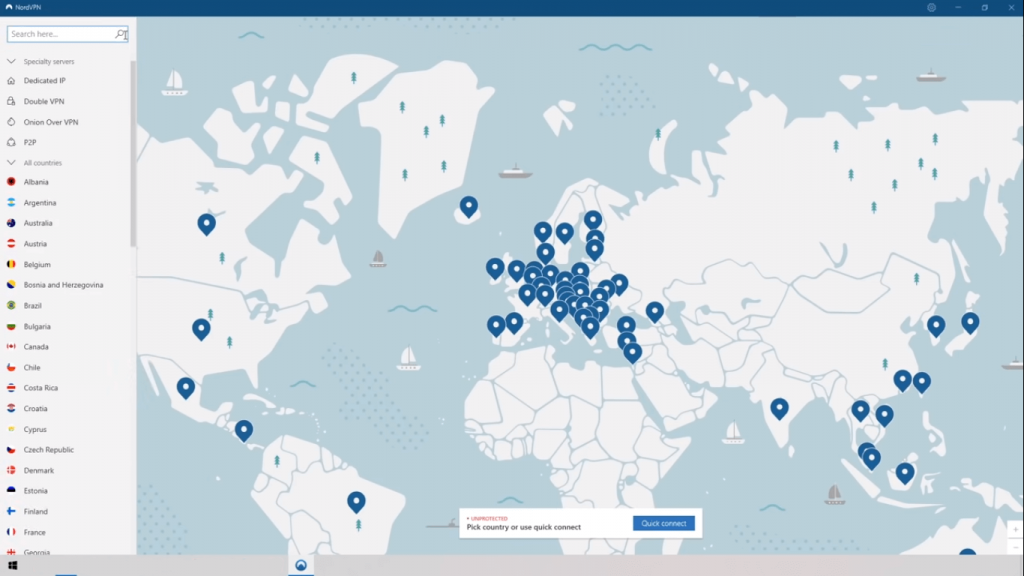
VPN (Virtual Private Network) is a powerful technology that exists in our society for decades. However, it didn’t make it to the limelight after the 2010s due to the excess internet consumption and government, corporate, ad networks, and invaders surveillance. VPN is a strong layer of protection for internet consumers, who want to secure the network, identity, and information from all prying eyes.
- VPN is a physical server in another country and your internet activity is masked by the physical server IP address.
- Your VPN provider will protect your information, so choose the provider wisely.
- You got plenty of locations, and you can select Asian, African, European, North American, and other countries.
- Your IP address & browsing activity is hidden from the world including the government.
If you choose NordVPN or other secure providers, then your security is guaranteed, and nobody can steal information or track internet activity.
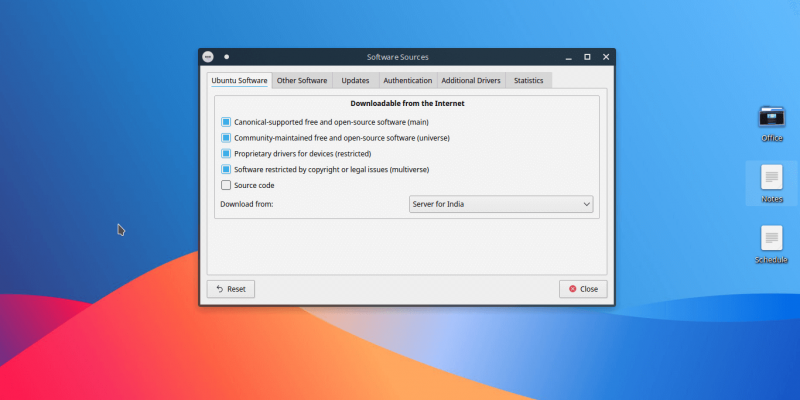
2. Use Updated Operating System & Software
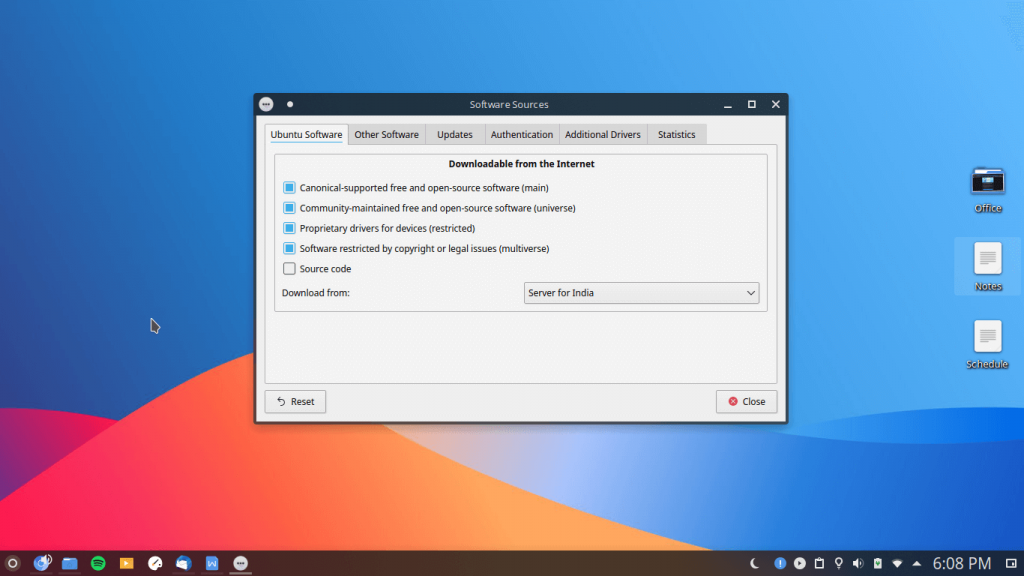
Most of the employees have MacBook, iMac, Windows, and Linux based computers. You may have been receiving software updates frequently, which is a good feature to have in modern computers. You should not miss one single security update because they are important to patch up the loopholes in the software. Make sure that you have devsecops to introduce security as a requirement at the start of the software development pipeline and delivery cycle.
Microsoft & Apple is pushing a lot of essential security updates, so do not skip them. Canonical is pushing security updates for Ubuntu 20.4 based computers, and you should miss out single update. Make sure to keep the programs up-to-date for maximum compatibility and security.
Note: Windows 10 (2004 build version) have a lot of bugs & glitches, so make sure to read online reviews before installing it.
3. Use secure cloud storage
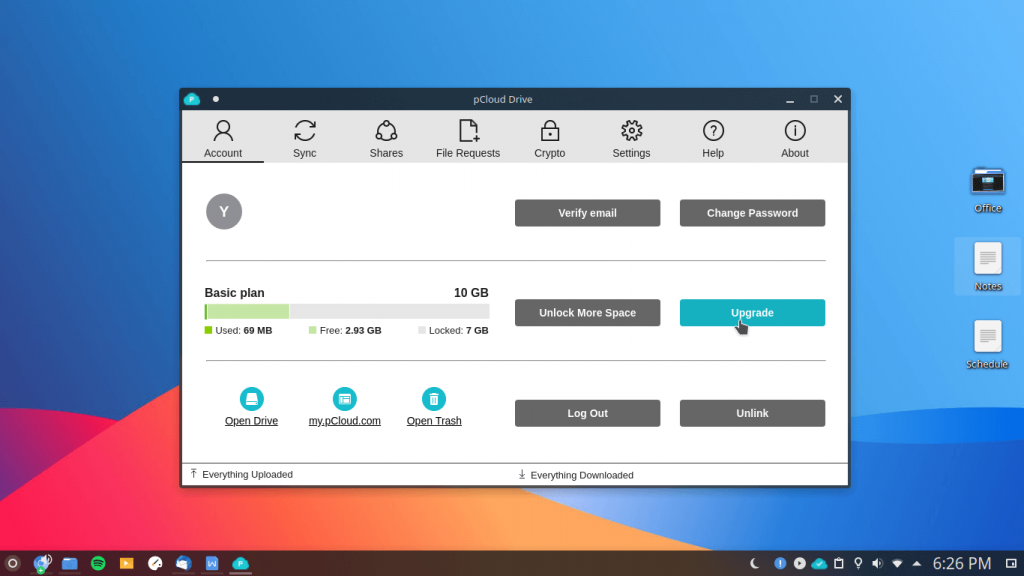
Nowadays, modern computers come with higher amount of storage options and 1TB SSD storage is the new standard. However, it is a good habit to upload important files & documents to cloud storage for many contributing reasons.
- Majority of the cloud storage providers like Apple, pCloud and other companies have strong policy against government surveillance and Data Sharing Laws.
- Cloud storage have strong protection layers to protect the users from all sorts of threats.
- Your data will never corrupt or go missing in the cloud storage until or unless, you make a mistake.
- Online cloud storage have strong servers, which will keep the data secure, so there is no chance of hardware failure.
Customers have a lot of free cloud storage services available in the market. If you want the information & data secure then choose European-based providers as Europe have strong Data Protection Laws.
4. Use Safe Collaboration Tools
Many employees have switched to Google Mail, Facebook, WhatsApp, and other social media platforms. However, we don’t recommend social media for communication and you can take collaboration Zoom video conferencing service for instance. Zoom has many loopholes and they have been in controversy surrounding privacy and security subject. You should secure & safe collaboration tools like Discord, Slack, Flowdock, etc. Then also look into virtual offices, as they are a great way of getting much more privacy if you work from home (so not having to put your personal home postal address on your web site) and you can also get a really cool city address like London. To do that just use a service like Virtual Office London, it’s so simple and low cost so well worth doing.
Note: Make sure to read news regarding the service.
5. Linux OS
Millions of computers are the primary target of hackers & invaders because it is easy to penetrate Windows & macOS machines. You have to opt-in antivirus systems and follow security protocols to prevent invasions, but it is 100% bulletproof at all, just like the materials from https://firebarrierexperts.com/mobile-and-accessible-barriers/.
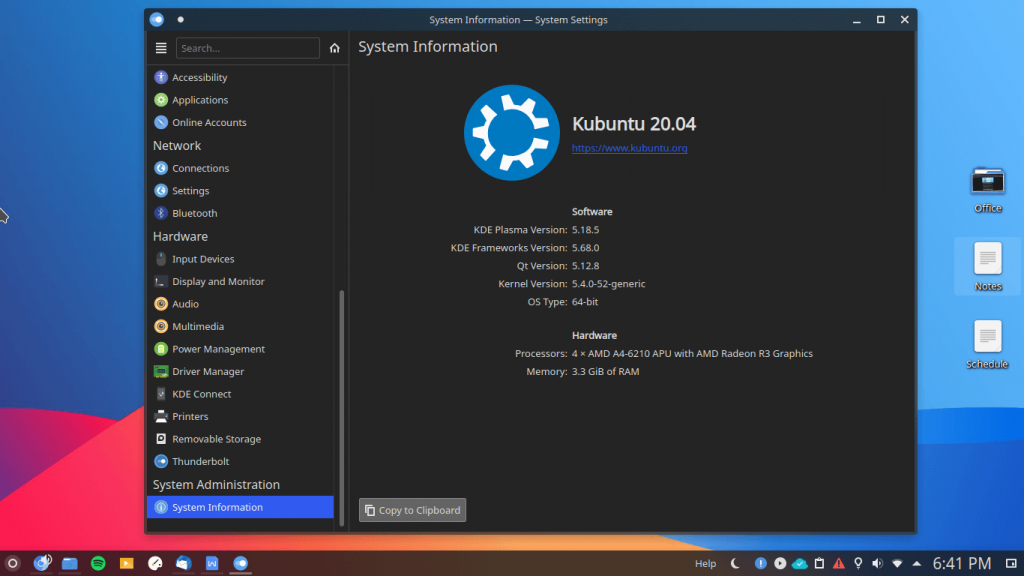
Amidst of all, the Linux operating system is a savior for millions of business people, developers, and employees. You can take Fedora, OpenSUSE, Ubuntu, CentOS, Oracle Linux, ClearOS, and more. Laptop or desktop administrators don’t have to worry about security as it is difficult to penetrate Linux security walls. You can try to know more about firewalld on CentOS, just visit this helpful site https://www.linode.com/docs/guides/introduction-to-firewalld-on-centos/. We also have been testing the Ubuntu-based operating system for a while, and it has a strong layer of protection.
Note: You have to spend a few minutes to find an ideal Linux OS because there is one designed for specific users.
Bottom Line
Readers can opt for antivirus solutions but they take a lot of control of the machine and keep a track of the activity. We don’t recommend most of the American-based software because they are infamous for stealing citizens’ data. Let us know what do you think about our recommendations in the comment section below.